TABLE OF CONTENTSFreshservice Alert Management enables ITOps & NOC Teams to oversee the status of the IT infrastructure issues from within their IT service desk. Freshservice Alert Management tackles noise, provides a real-time view of alerts on a single pane of glass, and automates incident creation, routing, and resolution. Here’s a bird’s eye view of how it is done.
Notifications from all monitoring tools are piped into Freshservice using webhooks
The payload is standardized by mapping the values used by monitoring tools to the ones used within Freshservice
Noise is reduced by grouping notifications from a common resource and with a common metric
The swarm of signals sent by multiple monitoring tools is thus filtered to extract a list of alerts on a single pane of glass
Algorithmically defined conditions drive automated conversion of alerts into incidents, and their resolution
Such algorithmically defined conditions also automatically route incidents to agents and agent groups
Users with sufficient number of resources and alerts qualify for advanced noise reduction features using Freddy Machine Learning algorithm
Integration of monitoring tools in Freshservice
While Freshservice offers out-of-the-box integrations with a growing list of popular monitoring tools, it can integrate with any tool in the world using webhooks.
In either case, the payload is normalised and severity values mapped to Freshservice values. Establishing a common standard to interpret notifications from multiple monitoring tools has dual benefits:
Users are able to comprehend issues faster
Freshservice is able to detect correlation between notifications from different monitoring tools and with other varying metadata to identify underlying issues faster
Noise reduction in Freshservice
Freshservice reduces noise in three ways to simplify alert management:
Basic grouping: Notifications from monitoring tools are grouped together on the based on any combination of Resource name, Metric name, Message, and Node by creating a custom integration. by default, all notifications are grouped by Resource name and Metric name. For instance, all the notifications about the capacity of server A would be grouped together. This helps suppress noise from repetitive and duplicate alerts. In Freshservice, a group of such notifications is referred to as an alert.
Machine Learning based Automated Grouping: Freddy, the Machine Learning algorithm, studies the historical patterns between alerts and associated incidents. Based on those patterns, Freddy attaches relevant incoming alerts to open incidents. Doing so preempts the unnecessary creation of a new incident while making an existing incident contextually richer. In Freshservice, we refer to this strategy as Automated Grouping.
Manual association of an alert with an open incident: An alert can also be manually attached to a relevant open incident. This not only reduces noise at the incident level, but also trains Freddy ML algorithm to learn from this behaviour in accounts for which it is enabled.
Accessing Alerts within Freshservice
Once you’ve set up Alert Management, Freshservice will start receiving notifications from your monitoring tools. These notifications are treated for noise reduction, after which alerts are displayed on the Alerts List page which can be accessed by clicking on the Alerts icon on the left nav bar.
View all open alerts under the Alert ID column. Each alert has an associated subject, severity, last updated details, the resource, and the associated incident if any.
Use the filter option on the top right corner to filter alerts based on created date, severity, resource, suppression status, etc. 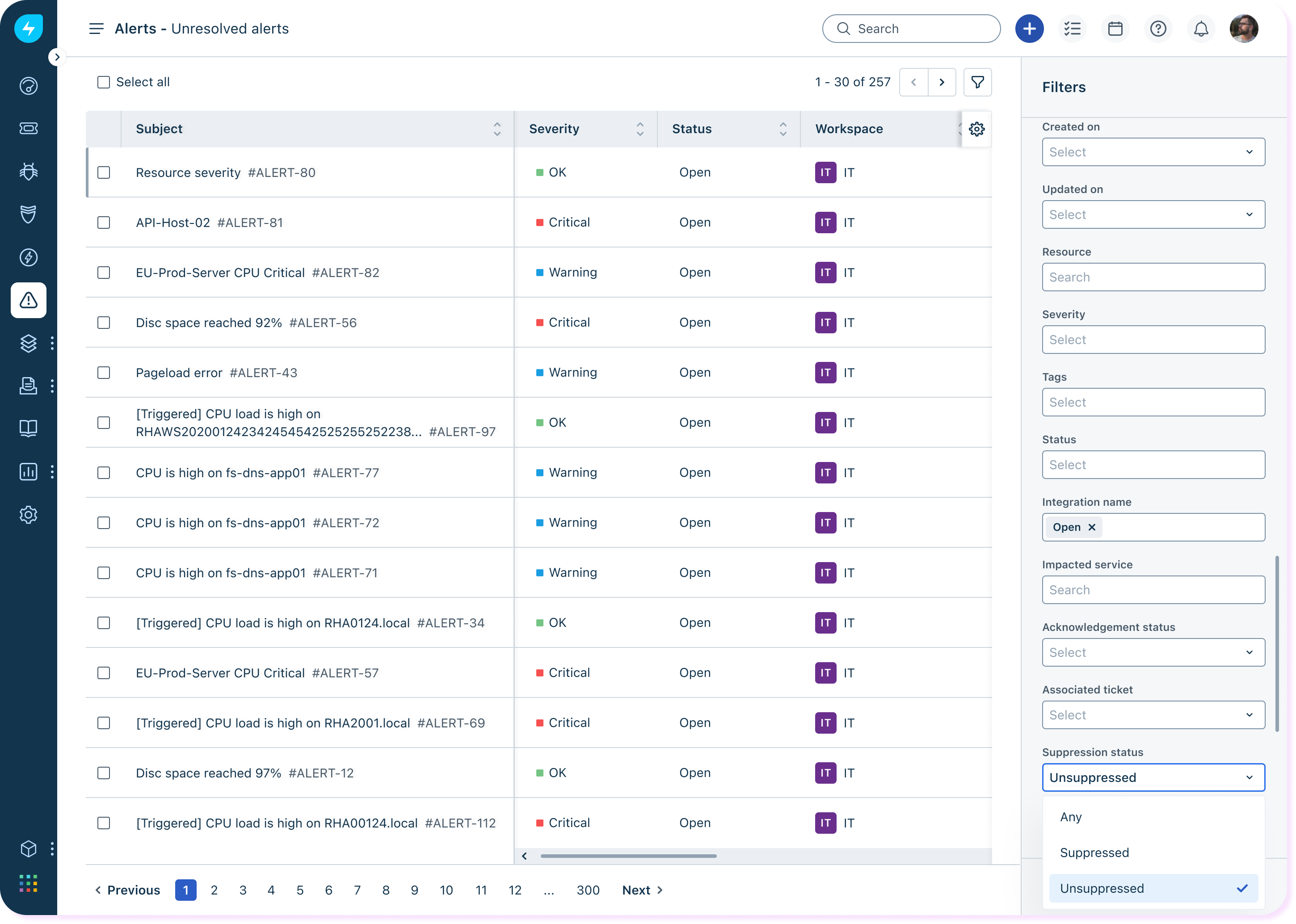
Incident creation and resolution
Freshservice enables automatic creation and resolution of Incidents based on Alert Workflows. An Alert Workflow offers nested if-then-else rules in a single automator. You can specify precisely when a workflow should run, either when an alert is created or updated. You can choose to trigger workflows if the severity is updated to certain value or if the alert status changes. You can also assign incidents created from an alert directly to specific agents and/or agent groups based on predefined criteria.
Alert reporting & analytics
Use the Analytics section to get a granular view of your digital infrastructure. Explore the system-curated Alerts report. Get a visual snapshot of alerts and incidents created over the past 30 days, the resources generating the most alerts, and more. Create your own custom report if you are keen to dig deeper.
Now that you are familiar with the concept of Alert Management in Freshservice, check out these related resources to start making the most of this feature:
- How to set up Alert Management in Freshservice
- Learn how to use alerts in Freshservice Alert Management
- Glossary: Alert Management in Freshservice


